KYC basically verifies and authenticates the validity of clients by asking, “Are you who you say you are?” As a consumer, are you safe to work with? The acronym for “Know Your Customer” is “KYC.”
KYC Verification
To ensure the prevention of fraud and other financial crimes, it is an essential component of the customer due diligence process. Additionally, it is essential to maintaining the integrity of the larger global financial system, thus if a weakness or loophole is taken advantage of, the monetary ecosystem would suffer greatly.
The idea of vetting clients before starting a business connection is not new; the first Know Your Customer (KYC) regulations were developed in the US in the 1970s as a means of preventing money laundering and were enacted under the Bank Secrecy Act (BSA). Since then, this original structure has undergone revisions and changes, most notably as a result of the Patriot Act following the September 11th terrorist incident in 2001 and the 2008 financial crisis. KYC regulatory compliance has evolved symbiotically with the adaptations made to KYC procedures.
KYC Process
Business security has undergone a revolution thanks to proactive security measures, which also protect an organization’s reputation and prevent non-compliance penalties and financial losses. They also remove the danger of doing business with high-risk or fraudulent clients. Nonetheless, unauthorized access to online platforms is frequently the cause of fraudulent actions when they do occur, which is why KYC is essential for preventing fraud and has led to KYC compliance.
Automate your KYC Process & reduce Fraud!
We have helped 1000+ companies in reducing their user onboarding TAT by 95%
Process for KYC Verification
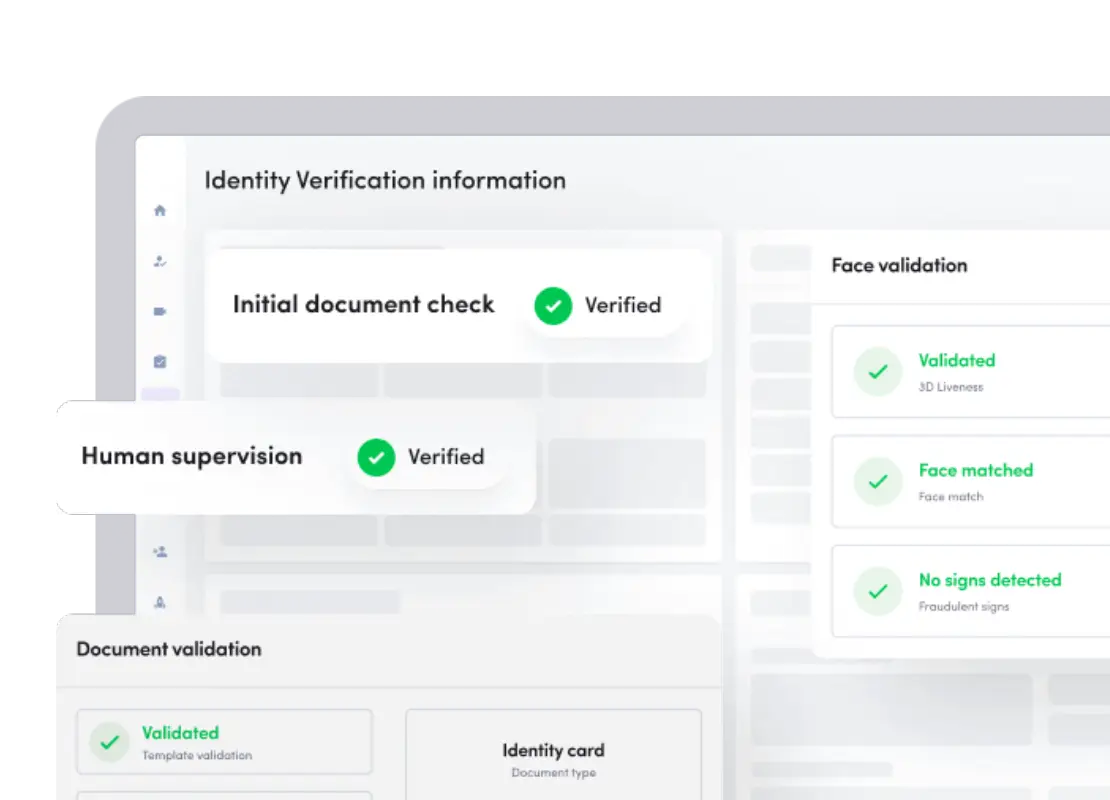
The processes involved in e-KYC are comparable to the conventional KYC procedure that was formerly used by banks using in-person and paper verification.
Step 1: Information gathering
The company must obtain the appropriate personal data from the internet user as the first step in getting to know your consumer. This frequently occurs in the early phases of account registration, when registering requires personal information.
Step 2:Invite the user to submit evidence
To verify their identification, the user will be required to upload a piece of supporting documentation. This stage covers a broad range of document types and might include face, address, and document verification. This is done to verify that the data supplied by the user is accurate.
Step 3:Information verification
The document template is recognised and scrutinized in accordance with a predetermined standard that conforms to international KYC compliance guidelines once the user submits a document as evidence. Online KYC verification software can identify forged papers and alert them for alteration or retouching. Data extraction occurs once document validity has been verified. Two methods exist for extracting data using Optical Character Recognition (OCR):
- Data extraction by optical character recognition (OCR): This method involves the system automatically extracting data from the identity document and verifying its legitimacy.
- Data extraction without optical character recognition (OCR):Without using OCR, data extraction is done manually by the user, and the IDV solution compares the information they provide with that on the identification paper.
Step 4: Programme for customer identification
The Customer Identification Programme is the next step in the KYC process (CIP). Ensuring the verification of the entity conducting a financial transaction is the mandate of CIP. This is required to stop money laundering, financing of terrorism, and other illicit activities that cause disruptions to the financial system as a whole.
Financial organizations must gather user data under CIP in order to create a bank account. This data consists of:
- Name
- Address
- Date of birth
Following collection, this data is checked against supporting documentation obtained through document or biometric verification. The crucial element of customer and business account risk assessment is also included in CIP, allowing financial institutions to create criteria that clients will be able to compare their risk scores against. Depending on the company and sector, this may change. This predetermined criterion helps avoid fraud, and the organization may now choose how to proceed with its Enhanced Due Diligence (EDD) and Customer Due Diligence (CDD) processes.
Step 5: Customers’ Due Diligence
This procedure involves checking a customer’s data against KYC guidelines. This is the second phase in KYC compliance, when online, real-time data collection of fundamental consumer information takes place. The data gathered for CDD comprises:
- Name
- Address
- Age
- Birthdate
The purpose of all this data is to validate the onboarding client. Following the AML screening process and financial credibility assessment, the consumer is rated based on their credentials. If a client’s ID is detected because of information on watchlists or PEP records, the customer is considered high-risk and the Enhanced Due Diligence procedure is initiated.
Customer Due Diligence evaluates a customer’s potential risk to an organization and should identify individuals who have previously participated in money laundering and terrorism funding.The nature of the business and the growing threat of financial crime will cause those in the private and offshore banking sectors to conduct CDD at deeper levels.
What is KYC Verification in Corporates?
Know Your Business, or “KYB,” is a procedure that guarantees the verification of corporate entities or firms you are dealing with. It is considered “corporate KYC” and is an essential component of KYC compliance. The industry is now placing a high priority on the rules and regulations pertaining to Ultimate Beneficial Owner (UBO) verification in an effort to forge ethical and lawful commercial partnerships as well as a clean client base.
KYC Process in Banks
Banks often include the following four essential components in their KYC policies:
- Customer Policy
- Customer Identification Procedures, also known as Customer Identification Programme (CIP), include data gathering, identification, verification, and a check of politically exposed persons and sanctioned lists.
- Risk assessment and management (as part of the KYC process, due diligence)
- Continuous observation and documentation
Surepass helps you to scale up your business up to 40% with our video KYC authentication system. It is smooth and has features like GPS Mapping, real- time, customizable and secured. Try our free demo to have better knowledge with our Video KYC.